
Doxxing (or doxing) refers to the act of collecting and sharing someone’s private information online without their permission, usually with malicious intent. This can include personal details like home addresses, phone numbers, emails, family information, or even business documents.
For companies and their leaders, doxxing can lead to harassment, embarrassment, reputational harm, or even physical security risks. High-profile individuals such as CEOs, board members, or public-facing employees are frequent targets because exposing their information often creates a larger impact.
According to recent cybersecurity reports, doxxing incidents targeting corporate executives and employees have increased by over 35% since 2023, as attackers exploit online exposure and social media to gather personal data. Security experts warn that this rise highlights the growing overlap between personal privacy and corporate risk.
Doxxing differs from insider leaks or other forms of targeted attacks because it typically relies on publicly available or easily obtainable information. However, the motive remains the same – to intimidate, disrupt, or damage. Common reasons attackers doxx organizations include reputational sabotage, extortion, intimidation, hacktivism, and competitive disruption.
In this blog, we will cover what doxxing is, how it works, real-world examples, and practical steps individuals and businesses can take to prevent it.
What Does It Mean to Be Doxxed?
Being doxxed means having personal, private, or sensitive information exposed online without consent, typically to harass, intimidate, or harm the targeted person or organization. For executives, employees, and board members, this deliberate exposure can have severe consequences that extend beyond the individual, affecting the company’s overall reputation and operations.
The impact of doxxing extends far beyond a single person. It can trigger widespread consequences for both individuals and the organizations they represent.
Risks for Executives, Employees, and Board Members
- Threats and Targeted Harassment: Doxxed individuals may face direct threats both online and offline – including abusive messages, coordinated harassment campaigns, and even threats toward their families or physical safety. According to a 2024 CrowdStrike threat report, C-level executives and HR heads have become frequent targets in impersonation and recruitment-related scams, underscoring how attackers exploit publicly available data to create trust-based traps.
- Reputational Damage: Attackers can use leaked information to spread false narratives or connect individuals to controversial topics, harming both their personal and professional image. Recent patterns observed in Verizon’s Data Breach Investigations Report (DBIR) show that reputation-driven attacks are rising, particularly against technology and finance sector leaders who have strong online visibility.
- Identity Theft and Fraud: Exposed information such as addresses, phone numbers, personal correspondence, or financial data can be used for identity theft, social engineering, or account takeover. The Cybersecurity and Infrastructure Security Agency (CISA) has warned that doxxing campaigns often serve as precursors to phishing or fraud attempts against corporate employees.
- Physical Security Risks: Revealing home or office addresses, routines, or identifying information puts executives and their families at real risk of stalking, swatting, or physical assault. This not only endangers personal safety but also creates operational and reputational challenges for organizations tasked with protecting their workforce.
Thus, organizations must treat executive and employee data protection as a core element of their cybersecurity and HR policies.
Consequences to Businesses
- Loss of Trust: Clients, investors, and the public may lose confidence in a company’s ability to safeguard its people and data, which can damage long-term relationships.
- Operational Disruption: Doxxing incidents can trigger mass harassment, false alarms, or safety concerns that disrupt daily operations – especially if key leaders are targeted or forced offline.
- Regulatory Scrutiny: Data exposures may draw the attention of regulators if privacy or compliance measures appear weak.
- Financial Losses: Costs can include legal fees, crisis communication, cybersecurity improvements, and even ransom or extortion payments related to doxxing-linked threats.
Sectors at Higher Risk
Certain industries are more prone to doxxing due to their public visibility, access to sensitive information, and the potential impact of data exposure. Attackers often choose targets whose data can generate media attention, financial gain, or ideological leverage.
- Technology: High executive visibility and controversial innovations often make tech firms targets. Companies driving innovation, especially in AI, data analytics, or surveillance technologies, often face backlash from activist groups or competitors, increasing their doxxing risk.
- Healthcare: The sector manages highly sensitive patient and employee information. Doxxing in healthcare can lead to privacy violations, regulatory penalties, and emotional distress. Attackers often target healthcare workers or executives to pressure organizations or exploit patient data for financial fraud.
- Financial Services: Banks, fintech firms, and investment institutions hold vast amounts of personal and financial data. Threat actors target these organizations to gain insider information, manipulate markets, or extort money through exposure threats.
- Public Sector: Government officials, regulators, and public servants are often doxxed for ideological or political reasons. Hacktivist groups may leak their personal details to protest policies, influence public opinion, or disrupt institutional credibility.
- Politically or Socially Visible Companies: Businesses frequently in the public eye face a higher risk of targeted doxxing. Attackers exploit public controversies to damage reputation, incite harassment, or mobilize online backlash.
Doxxing has become a serious digital threat capable of destabilizing organizations and endangering individuals at all levels of leadership. Effective prevention, monitoring, and response strategies are essential to reduce risk.
How Does Doxxing Work?
Attackers use multiple methods to gather and publish sensitive information. Even seemingly harmless data, when combined, can reveal more than intended.
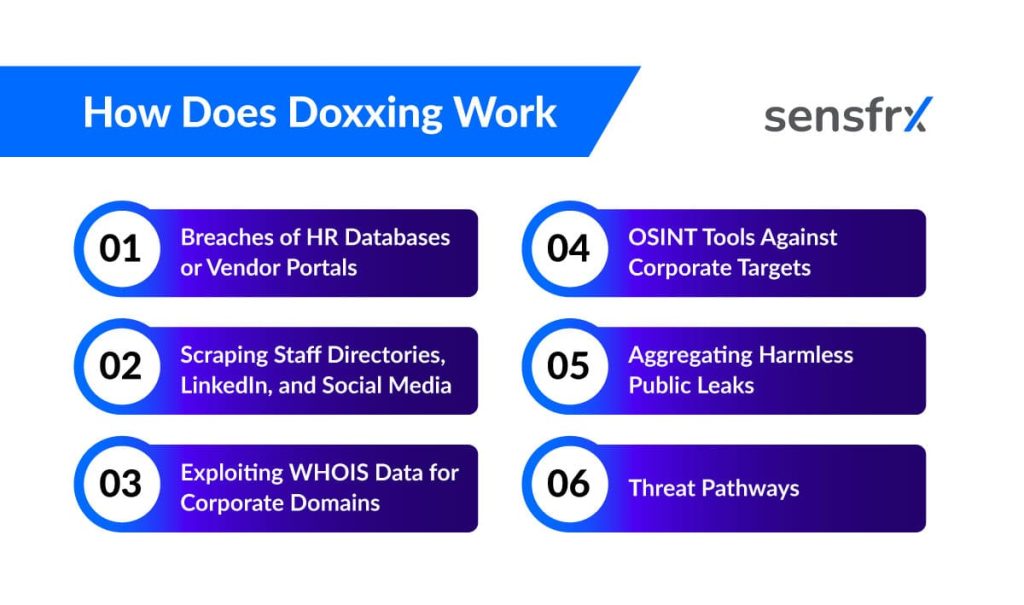
Here’s how it typically happens:
1. Breaches of HR Databases or Vendor Portals
Attackers may compromise HR systems or vendor portals to steal employee information such as names, emails, phone numbers, and job titles.
- Goals: Identity theft, executive impersonation, or financial fraud.
- Mitigations: Enforce MFA, apply least-privilege access, monitor login anomalies, and conduct vendor security audits.
2. Scraping Staff Directories, LinkedIn, and Social Media
Publicly available data can be gathered to map organizational structures and identify high-value targets.
- Goals: Crafting realistic phishing or social engineering campaigns.
- Mitigations: Limit public directory visibility, train employees to manage social media privacy settings, and monitor for mentions of company data online.
3. Exploiting WHOIS Data for Corporate Domains
WHOIS records may contain registrant names, phone numbers, and emails.
- Goals: Impersonation of domain administrators or phishing domain registrars.
- Mitigations: Use WHOIS privacy services, implement registrar-level account locks, and ensure domain-related communications are verified internally.
4. OSINT Tools Against Corporate Targets
Attackers leverage open-source intelligence (OSINT) tools to aggregate data from public sources such as GitHub, certificates, and job listings.
- Goals: Discover credentials, exposed subdomains, or internal policies.
- Mitigations: Conduct regular attack surface scans, sanitize public content, and review job postings for sensitive details.
5. Aggregating Harmless Public Leaks
Publicly available presentations, roadmaps, or employee bios can be pieced together to build convincing social engineering narratives.
- Mitigations: Review all external-facing materials and establish approval processes before publication.
6. Threat Pathways
Doxxing attempts may originate from:
- Unhappy Insiders: Individuals with legitimate access who leak internal data.
- Cybercriminal Groups: Financially motivated attackers leveraging leaked data for extortion.
- Hacktivist Collectives: Groups targeting organizations for political or ideological reasons.
Mitigations: Implement insider risk programs, secure telephony and authentication processes, and maintain a clear response plan for voice- or data-based incidents.
Doxxing Examples
Below are a few examples that illustrate how doxxing incidents unfold in real-world scenarios. These cases show how attackers use open-source intelligence (OSINT) methods to collect, connect, and publish information from multiple sources – a process that aligns with the MITRE ATT&CK framework’s “TA0043: Reconnaissance” phase.
This phase describes how threat actors gather publicly available data to identify potential targets and understand their digital footprint before launching an attack. In the context of doxxing, reconnaissance helps attackers compile scattered personal or corporate information into a single, detailed profile.
- Corporate Leadership Exposure: Company executives’ personal emails and phone numbers were leaked on social media, leading to harassment and extortion attempts. In most cases, attackers collect information from conference materials, company announcements, and LinkedIn activity, combining it with old breach data to build detailed executive profiles.
- Third-Party Data Breach: A vendor’s compromised system exposed employee data from multiple clients, which was later published online. Attackers often merge this type of information with publicly available details, expanding the scope of exposure and using it for impersonation, fraud, or targeted phishing attempts.
- Public Campaigns: Activist groups doxx organizations to expose confidential M&A plans or influence corporate decisions. These campaigns usually begin with small, overlooked details which are later aggregated through OSINT tools to create a broader narrative.
Analysts note that doxxing rarely results from a single incident. Instead, it is often the outcome of multiple small leaks and public disclosures that, when combined, form a complete picture of a target. This gradual information buildup can quickly escalate into a reputational and operational crisis if not detected early.
How to Prevent Doxxing in B2B
Preventing doxxing in business environments requires a blend of policies, awareness, and technology. Since attackers often exploit publicly available data or human error, organizations must take a proactive and layered approach to protection.
1. Develop Organizational Policies
Establish clear internal policies that limit what employee or executive information can be shared publicly. This includes restricting the publication of personal contact details, direct email addresses, and identifiable photos in press releases or corporate announcements. A well-defined policy helps maintain consistent standards across departments and prevents accidental data exposure.
2. Conduct Regular Digital Audits
Regularly review your organization’s online footprint (company websites, social media accounts, and third-party platforms) to identify and remove unnecessary or outdated personal information. Audits should also include domain registries, public repositories, and media kits that might reveal internal or employee data unintentionally.
3. Train Staff and Executives
Human error is one of the most common causes of doxxing exposure. Provide periodic training to educate employees and executives on social engineering, phishing attempts, and oversharing risks. Real-world examples of doxxing incidents can help them understand the severity and encourage responsible online behavior.
4. Enable WHOIS Masking and Continuous Monitoring
Use WHOIS privacy services to hide domain registration details that could expose admin contacts or company email addresses. Implement continuous monitoring tools to detect mentions of employee or company information on the dark web, data leak forums, and social platforms. Early detection allows for swift containment before attackers can exploit the data.
5. Strengthen Technical Controls
Use strong security measures to reduce information leakage. This includes enforcing multi-factor authentication (MFA), restricting access based on least privilege, securing email gateways, and regularly patching vulnerabilities across systems. Combining these measures significantly reduces the attack surface available to threat actors.
6. Establish an Incident Response Plan
Despite best efforts, incidents can still occur. Develop a crisis response plan that defines clear communication channels, escalation procedures, and roles during a doxxing event. The plan should include steps for verifying leaked information, notifying affected employees, involving legal teams, and coordinating with law enforcement if necessary. A well-prepared response minimizes panic, damage, and downtime.
Building a culture of privacy awareness and continuous vigilance strengthens organizational resilience against doxxing threats.
Legal and Ethical Implications for Businesses
Even with strong preventive measures, the legal and ethical landscape surrounding doxxing remains complex. Doxxing is considered a form of harassment, data privacy violation, and in some cases, corporate espionage. Organizations operating under data protection regulations like GDPR, CCPA, or local cybersecurity frameworks must ensure that personal and employee data is handled securely.
However, pursuing and prosecuting doxxers is often complex due to jurisdictional limitations and anonymity. Businesses should work closely with legal counsel and law enforcement agencies to navigate such cases effectively.
Conclusion
Doxxing represents one of the most personal and damaging forms of online attack – blurring the line between digital and physical security. For individuals, it can lead to harassment and emotional distress. For businesses, it can cause reputational and financial harm that lasts long after the incident.
By combining strong privacy practices, employee awareness, technical safeguards, and swift incident response, organizations can significantly reduce their exposure.
In today’s interconnected world, protecting sensitive information – whether personal or professional – isn’t optional. It’s a critical part of digital resilience and an essential step toward building lasting trust and security.
Want to safeguard your team and customers from attacks? Book a Sensfrx demo today and see how real-time fraud & threat detection can stop attackers before they strike.
FAQs
Details such as home addresses, phone numbers, personal or work emails, internal company documents, and even metadata from online posts can be exposed in a doxxing attack. For businesses, leadership contact details and employee directories are common targets.
Yes. When sensitive data is leaked, it damages customer trust and investor confidence. Even if no breach occurs, public exposure of private details can lead to negative publicity and long-term reputational loss.
Oversharing on social platforms gives attackers valuable information – from location tags to company updates. Aggregating these details helps them craft social-engineering schemes or identify employees for targeted harassment.
A doxxing response plan should outline steps for verifying exposed information, alerting affected employees, engaging legal and security teams, and managing public communication. Timely coordination limits panic, reputational fallout, and regulatory exposure.
Executives should restrict the visibility of personal data, use separate professional contact details, avoid sharing family or travel information publicly, and employ privacy tools such as domain masking and data-removal services.
Dark-web monitoring tools, data-leak detection services, and digital-footprint scanners can alert businesses when employee information appears in unauthorized sources. Combining these tools with regular audits enhances early threat detection.




