
Fraud in 2026 is becoming more advanced, with 41% of attacks now AI-driven. Activities like account takeovers, fake identities, and bot attacks are organized and automated. Traditional methods struggle as IPs change quickly, cookies disappear, and even authentication can be bypassed.
What businesses need is a way to recognize risk even when these signals change. Device fingerprinting helps by identifying suspicious devices early and stopping fraud before it grows.
Not as a marketing tool. Not as user tracking. But as device-level intelligence that reveals intent before fraud escalates.
Understanding Device Fingerprinting Beyond the Definition
Device fingerprinting creates a unique digital identifier for a device using a combination of hardware characteristics, software configurations, and behavioral signals. But defining it that way only scratches the surface.
In fraud prevention, device fingerprinting answers a deeper question:
Is this device trustworthy?
Every device interacting with your platform leaves signals. Screen resolution, CPU architecture, operating system, browser configuration, installed plugins, timezone, language settings, emulator indicators, and interaction patterns — individually these may appear insignificant.
Consider a user who signs up on your platform using a new email ID. A few minutes later, another account is created. Then another. Each time, the IP address is different and cookies are cleared, making every session look like a new user.
Combined, these signals form a highly distinctive profile.
Even though the fraudster keeps changing visible identifiers, the device characteristics—same screen size, same OS version, same browser quirks, same interaction patterns—remain consistent. This allows security systems to recognize that all these accounts are coming from the same underlying device.
And that is where fraud patterns begin to emerge.
Why Traditional Identification Methods No Longer Work Alone
Historically, fraud detection relied on session-based signals.
Cookies were used to track repeat visitors, IP addresses helped identify suspicious geolocations, and Usernames and passwords were treated as identity proof.
But today’s fraud ecosystem operates differently.
Fraudsters use residential proxy networks to appear legitimate. They deploy anti-detect browsers that mimic real environments. They automate credential stuffing attacks at scale. They create multiple accounts from the same physical device using virtualization tools.
The reality is simple:
- Traditional methods identify sessions.
- Modern fraud operates at the device level.
If ten accounts are created from one device but using different IPs, cookies, and email addresses, session-based detection may fail. Device intelligence does not.
How Device Fingerprinting Works in a Fraud Prevention Framework
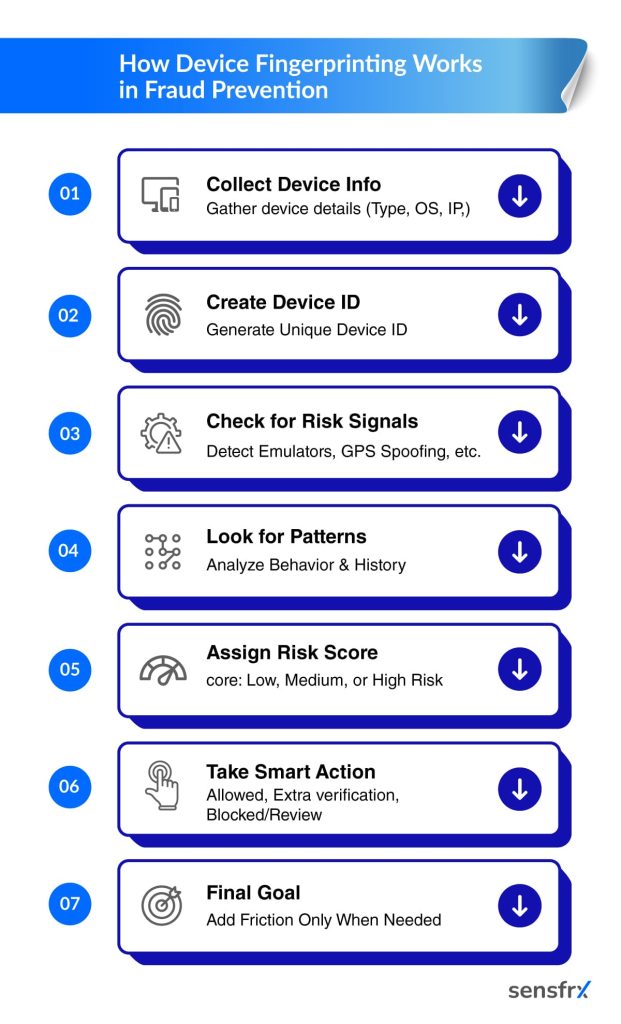
Device fingerprinting is not a one-step process. It operates as part of a broader risk evaluation architecture.
The first stage involves device identification. A unique alphanumeric Device ID is generated by analyzing a combination of attributes. This identifier remains relatively stable across sessions, even when superficial data changes.
The second stage involves risk signal detection. The system evaluates whether the device shows signs of manipulation. These may include emulator environments, rooted or jailbroken status, app cloning frameworks, GPS spoofing tools, automation scripts, or abnormal configurations.
None of these signals alone confirm fraud. However, fraud rarely depends on a single indicator. It depends on patterns.
The final stage involves dynamic risk scoring. Based on historical associations, number of linked accounts, behavioral anomalies, and severity of detected signals, the device is assigned a risk score.
This enables intelligent decisions:
- Allow low-risk interactions seamlessly
- Trigger step-up authentication for medium-risk scenarios
- Block or review high-risk devices instantly
The goal is not to block aggressively. The goal is to apply friction intelligently.
Core Components That Strengthen Device Intelligence
Device fingerprinting becomes powerful when multiple layers of intelligence work together.
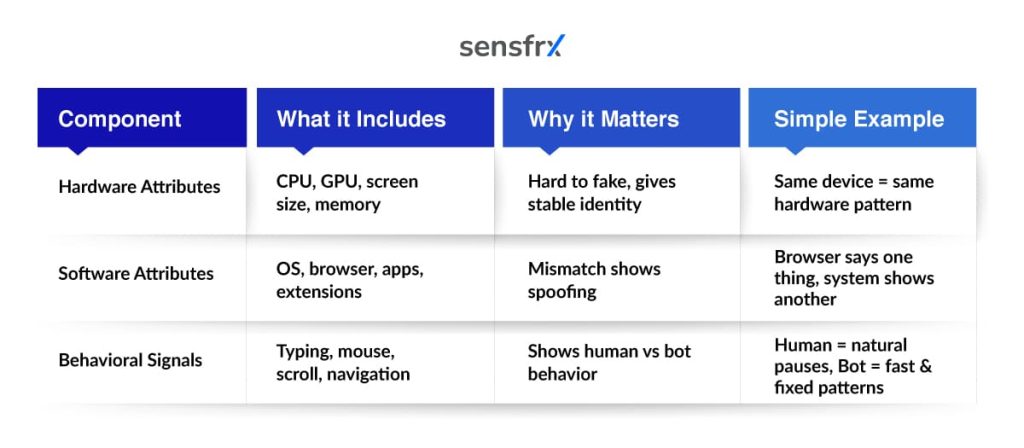
1. Hardware Attributes
Hardware-level signals such as CPU type, GPU configuration, screen dimensions, and memory specifications provide structural stability to a fingerprint. These attributes are difficult to manipulate without changing the physical device itself.
Fraudsters can spoof IP addresses. Recreating an entire hardware environment consistently is far more complex.
2. Software Attributes
Operating system versions, browser types, installed extensions, and application builds provide contextual depth. Inconsistencies between hardware and software layers often reveal attempts at spoofing or automation.
For example, a browser claiming one configuration but operating within a virtualized environment raises immediate red flags.
3. Behavioral Signals
Behavioral fingerprinting adds a dynamic layer. Typing cadence, mouse movement, interaction timing, scroll patterns, and navigation behavior help distinguish real users from automated activity.
For Example: A genuine user types with natural pauses, moves the mouse unevenly, and scrolls at varying speeds. A bot, on the other hand, may type instantly, click in fixed patterns, and navigate pages with mechanical precision.
Automation scripts can mimic clicks and basic actions, but they often fail to replicate these natural interaction rhythms.
When this behavioral data is combined with device signals like hardware and software characteristics, detection becomes far more reliable. Let us try to take an example to understand it better. A login attempt comes from a known device, but the typing speed is unnaturally fast and navigation is too perfect and this mismatch signals potential automation or account takeover.
When hardware, software, and behavior are analyzed together, detection confidence increases significantly.
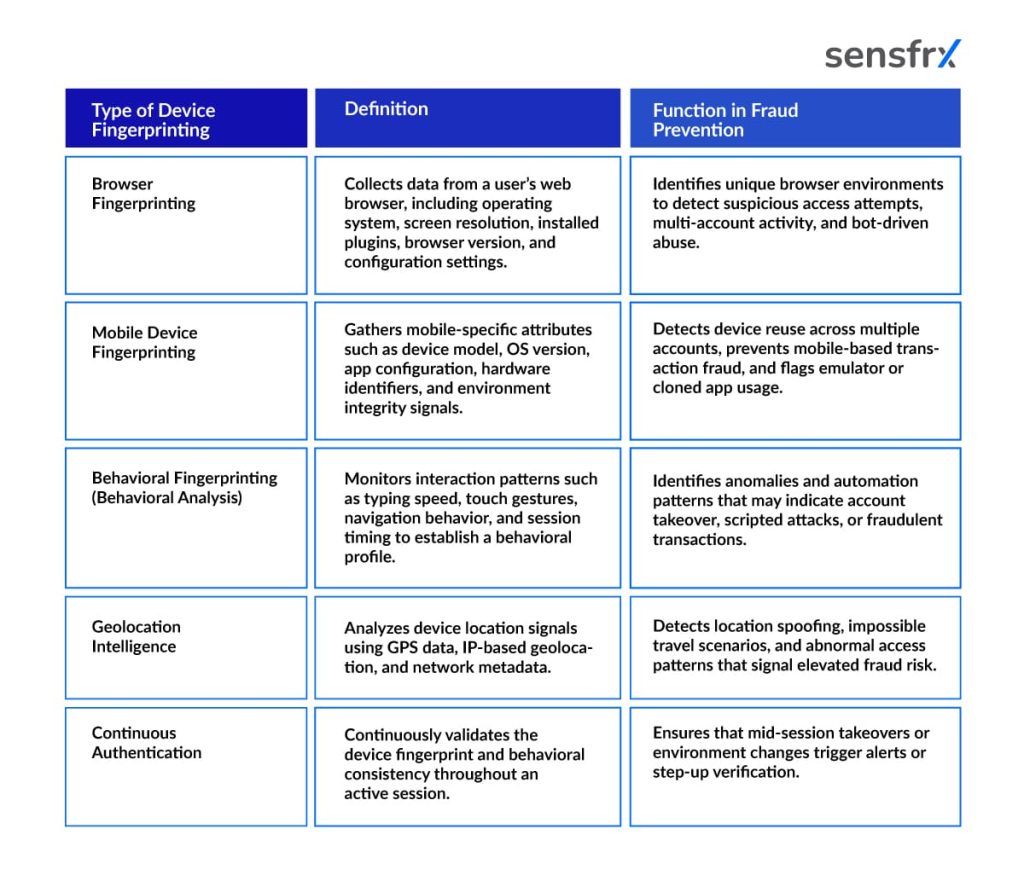
Types of Device Fingerprinting
Device fingerprinting is not a single technique. It operates through multiple layers, each designed to capture different dimensions of device and user interaction.
Some methods focus on browser-level attributes. Others analyze mobile-specific signals. Advanced implementations extend into behavioral monitoring and continuous validation throughout the session.
Understanding these types helps organizations determine how deeply they want to integrate device intelligence into their fraud prevention framework.
Where Device Fingerprinting Delivers Strategic Impact
- During account registration: Identifies multiple accounts created from the same device.
Example: One device signs up with 5 different emails to claim a signup bonus.
- During login attempts: Detects unfamiliar or high-risk devices trying to access accounts.
Example: A user usually logs in from Pune, but suddenly a new device attempts access from a different setup.
- During transactions: Device reputation feeds into real-time risk decisions.
Example: A payment is initiated from a device previously linked to failed or fraudulent transactions.
- In BNPL environments: Prevents repeated installment abuse from the same device.
Example: One device creates multiple identities to bypass credit limits.
- In online gaming and promotions: Blocks multi-accounting and bonus abuse.
Example: A player creates multiple accounts from one device to repeatedly claim rewards.
- In crypto and trading platforms: Identifies coordinated activity across linked fraudulent accounts.
Example: Multiple accounts executing similar trades from the same device pattern.
The true value lies in continuous monitoring, not in one checkpoint.
Privacy, Compliance, and Responsible Implementation
Device fingerprinting must be deployed responsibly.
Regulations such as GDPR emphasize transparency, purpose limitation, and data minimization. Organizations must ensure device data is collected strictly for security purposes and stored securely.
Encryption, retention controls, and clear privacy policies are essential. The objective is fraud prevention, not user surveillance.
When implemented with governance and accountability, device fingerprinting strengthens security without compromising compliance.
Implementation Challenges and Considerations
While powerful, device fingerprinting is not a silver bullet.
Sophisticated fraudsters use anti-detect browsers and device spoofing tools. Static fingerprint models may degrade over time as device configurations change naturally.
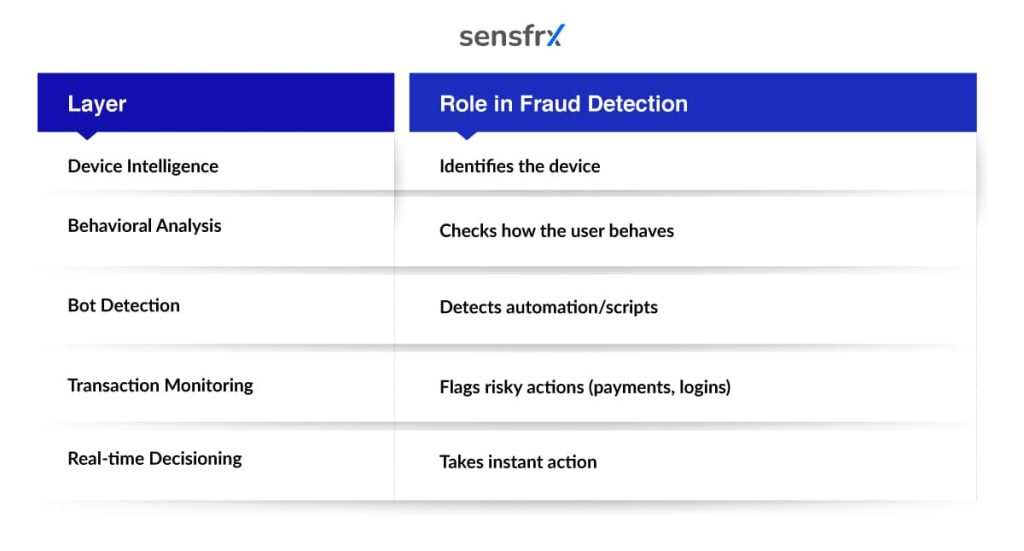
This is why device fingerprinting must be adaptive.
Risk models must continuously recalibrate. Device intelligence must be integrated with behavioral analytics, bot detection systems, transaction monitoring engines, and real-time decisioning frameworks.
Organizations that treat device fingerprinting as a standalone solution often underutilize its potential. It is most effective when it becomes part of a layered fraud prevention strategy.
How Sensfrx Enhances Device-Level Fraud Intelligence
At Sensfrx, device fingerprinting operates as part of a broader real-time risk engine.
Instead of simply identifying devices, the platform analyzes device attributes alongside behavioral signals, transaction context, and historical activity.
This allows businesses to:
- Detect high-risk devices before transactions complete
- Prevent account takeover attempts early
- Reduce chargebacks linked to repeat device abuse
- Block bot-driven registrations and automation
- Minimize false positives through adaptive scoring
Fraud prevention today is not about collecting more data, it is about interpreting signals intelligently.
Device fingerprinting becomes truly effective when it is part of an ecosystem that understands intent.
Conclusion
Fraud is no longer limited to stolen credentials or suspicious transactions. It is increasingly device-driven, automated, and coordinated across multiple accounts and touchpoints.
As fraud tactics evolve, relying solely on IP tracking, cookies, or static rules leaves critical gaps in detection. Businesses need deeper visibility — not just into who is accessing their platform, but from which device and with what intent.
Device fingerprinting provides that persistent layer of intelligence. When combined with behavioral analysis and dynamic risk scoring, it helps organizations detect patterns early, prevent repeat abuse, and reduce fraud losses without disrupting genuine users.
At Sensfrx, device intelligence is not treated as a standalone feature. It is integrated into a real-time fraud prevention framework that analyzes multiple signals, identifies high-risk behavior instantly, and enables smarter decision-making across the customer journey.
If your organization is looking to strengthen fraud defenses without adding friction, it may be time to rethink how devices are evaluated within your security architecture.
Explore how Sensfrx can help you detect and prevent fraud proactively. Book a demo to see device intelligence in action.
Frequently Asked Questions (FAQs)
IP tracking identifies network location, which can change frequently. Device fingerprinting analyzes device-level attributes that remain more stable and harder to manipulate.
Advanced attackers may attempt spoofing, but multi-layered fingerprinting combined with behavioral analysis significantly reduces bypass success rates.
When optimized correctly, it operates in the background and does not introduce noticeable friction for legitimate users.
Yes, when implemented with transparency, data minimization, encryption, and proper governance aligned with regulations such as GDPR.
No. It delivers maximum effectiveness when integrated with behavioral analytics, bot detection, and real-time risk scoring systems.


