
Account takeover (ATO) attacks have become one of the most damaging and persistent threats facing digital businesses today. Unlike traditional breaches that rely on exploiting software vulnerabilities, ATO attacks target something far more fragile – user trust.
When attackers gain access to legitimate user accounts, the impact goes far beyond unauthorized logins. Stolen funds, fraudulent transactions, data exposure, regulatory penalties, and customer churn often follow. These attacks can bypass traditional security controls because attackers frequently use valid credentials.
This is why organizations are shifting their focus from simple authentication controls to dedicated account takeover prevention tools designed to detect malicious behavior even when everything appears normal.
In this blog, we will explore what ATO attacks really look like, why traditional defenses fall short, what to look for in an ATO prevention solution, a detailed comparison of the top ATO tools, and best practices to build a layered, future-proof defense.
What Is an Account Takeover (ATO) Attack?
An account takeover attack occurs when an unauthorized user gains access to a legitimate user account and uses it for fraudulent or malicious purposes. Unlike brute-force attacks, modern ATO attacks often succeed without triggering obvious alerts.
Once breached, attackers can:
- Perform fraudulent transactions
- Change account credentials to lock out users
- Steal personal or financial/sensitive information
- Abuse loyalty points or stored payment methods
- Use compromised accounts to launch further attacks
The most dangerous aspect of ATO attacks is that they look like real users behaving normally.
How Account Takeover Attacks Work in Practice
Most account takeover attacks look legitimate. By leveraging valid credentials and realistic session behavior, attackers can bypass basic security checks and operate undetected until misuse or fraud occurs.
Common techniques include:
1. Credential stuffing: Attackers reuse usernames and passwords leaked from previous data breaches, relying on password reuse across platforms. Even a low success rate becomes effective when tested against thousands of accounts.
2. Brute-force and password spraying: Instead of guessing many passwords for one account, attackers try a small set of common or predictable passwords across many accounts. This approach helps them avoid lockouts while increasing the chance of compromise.
3. Phishing and social engineering: Users are tricked into sharing credentials through fake emails, messages, or look-alike login pages. These attacks often bypass technical defenses by exploiting trust rather than system weaknesses. Learn more about how to prevent phishing attacks.
4. Bot-driven login abuse: Bots simulate real browsers and human behavior, including mouse movements and timing patterns. This allows them to evade basic bot detection, CAPTCHAs, and simple rate-limiting controls. Because credentials are often valid, traditional controls like password checks or basic rate limiting are no longer enough.
Why Traditional Security Controls Are Not Enough
Many organizations still rely heavily on foundational security controls such as:
- Password policies
- CAPTCHA challenges
- Static multi-factor authentication (MFA)
These measures are important, but they are not designed to handle today’s automated and behavior-mimicking attacks. Modern attackers use valid credentials, rotate IPs, simulate human behavior, and distribute login attempts across accounts. As a result, traditional controls face clear limitations:
They create friction for legitimate users: Frequent password resets, repetitive CAPTCHA challenges, and unnecessary MFA prompts can negatively impact user experience and increase drop-offs.
They can be bypassed by advanced bots: Automated tools can evade basic CAPTCHA systems, mimic browser behavior, and avoid simple rate-limiting rules.
They struggle to detect post-login misuse: Once a user is logged in, traditional controls usually stop monitoring activity. They do not track what happens inside the session, where most fraud and data misuse actually occur.
They generate false positives at scale: Rigid rules often flag genuine users as suspicious, especially in high-traffic environments, leading to operational strain and customer frustration.
This is where account takeover prevention tools add value. Instead of relying only on credentials alone, they evaluate behavior, device intelligence, and contextual risk in real time, enabling accurate detection without unnecessary disruption.
What to Look for in an Account Takeover Prevention Tool
Not all security solutions are built for ATO prevention. An effective tool should go beyond basic authentication controls and focus on detecting real attack patterns without disrupting legitimate users.
An effective ATO prevention tool should provide:
- Real-time detection, not just alerts
- Behavioral analysis to identify abnormal activity
- Device and session intelligence
- Bot and automation detection
- Low false positives to protect user experience
- Scalability for high-traffic environments
With these criteria in place, organizations can evaluate solutions based on practical capabilities rather than feature lists alone. Let’s examine the leading ATO prevention tools available today.
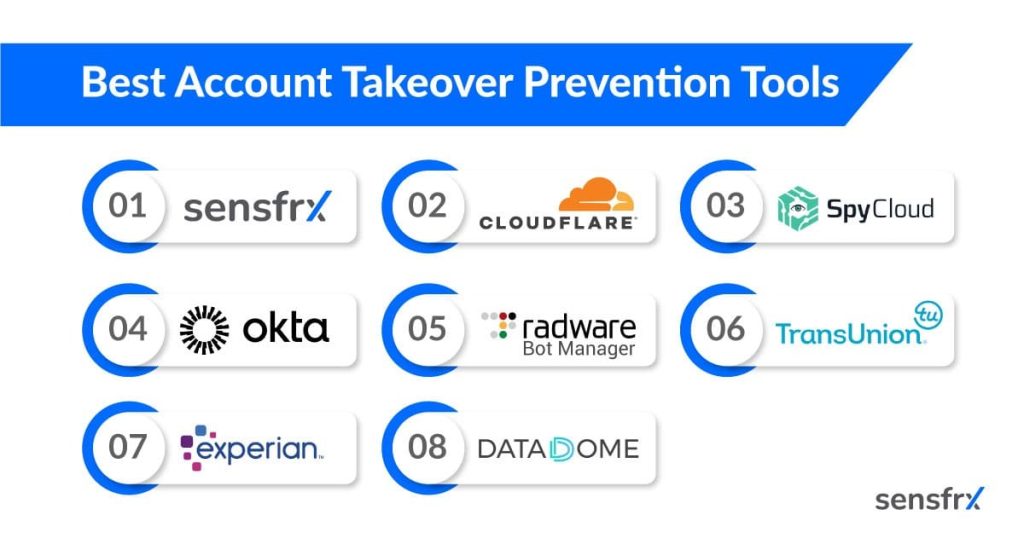
Top 8 Account Takeover Prevention Tools
1. Sensfrx
Sensfrx is a specialized account takeover prevention platform built to detect credential abuse, bot-driven attacks, and suspicious account behavior in real time. It helps accurately distinguishing between genuine users and attackers, even when valid credentials are used.
Rather than relying on static rules, Sensfrx continuously analyzes device signals, behavioral patterns, and session context to make high-confidence decisions without disrupting legitimate users.
Key Features
- Advanced device fingerprinting
- Behavioral and session risk scoring
- Detection of credential stuffing and brute-force attempts
- Bot and automation identification
- Real-time response with minimal latency
Pros
- Effective against both bots and human attackers
- High-accuracy fingerprinting
- Real-time, delay-free analytics
- Seamless integration across various platforms
- Fast decision, implementation, and response time
- 99.9% uptime of APIs & services
- Very low false-positive rates
2. Cloudflare

Cloudflare provides account takeover protection as part of its broader bot management and application security platform. It leverages global traffic visibility to detect automated login abuse and anomalous behavior at the network edge.
Key Features
- Network-level bot intelligence
- Behavioral anomaly detection
- Rate limiting and challenge mechanisms
- Integrated WAF and CDN protection
Pros
- Excellent scalability
- Strong protection against high-volume automated attacks
- Easy deployment for existing Cloudflare users
Cons
- Limited insight into post-login user behavior
- Less specialized for nuanced ATO detection
3. SpyCloud

SpyCloud takes a proactive approach by focusing on credential exposure intelligence. It monitors underground sources for stolen usernames, passwords, and session data, helping organizations act before those credentials are abused.
Key Features
- Dark web and breach monitoring
- Credential exposure alerts
- Automated remediation workflows
- Identity exposure analytics
Pros
- Prevents attacks before they happen
- Strong visibility into compromised identities
- Excellent complement to real-time detection tools
Cons
- Does not block attacks in real time
- Requires integration with IAM or SOC processes
4. Okta
Okta offers ATO protection through adaptive authentication and contextual access controls. It evaluates login risk based on user behavior, device, and location, applying MFA only when necessary.
Key Features
- Risk-based MFA
- Device and location intelligence
- Login anomaly detection
- Centralized identity management
Pros
- Strong enterprise IAM capabilities
- Well-suited for workforce and B2B environments
- Flexible access policies
Cons
- Not purpose-built solely for ATO prevention
5. Radware – Bot Manager
Radware Bot Manager focuses on blocking automated attacks at scale. It is particularly effective against credential stuffing and scripted login abuse.
Key Features
- Bot behavior fingerprinting
- Real-time bot mitigation
- Challenge-response mechanisms
- Detailed attack analytics
Pros
- Strong automated attack protection
- Reduces infrastructure strain
- Customizable mitigation strategies
Cons
- Limited detection of human-driven fraud
6. TransUnion
TruValidate combines identity intelligence with behavioral analytics to assess login and transaction risk. It is commonly used in financial services and regulated industries.
Key Features
- Identity-based risk scoring
- Behavioral analytics
- Transaction monitoring
- Compliance-ready reporting
Pros
- Strong identity verification capabilities
- Suitable for regulated environments
- Covers both login and transaction risk
Cons
- Complex integration
- Higher cost for smaller organizations
7. Experian
Experian leverages identity and credit data to enrich fraud detection signals, helping organizations assess account access risk more accurately.
Key Features
- Identity and credit intelligence
- Suspicious login detection
- Fraud scoring APIs
- Compliance support
Pros
- Strong trust signals
- Widely used in financial services
- Regulatory alignment
Cons
- Less effective against advanced bot attacks
- Heavier operational overhead
8. DataDome
DataDome specializes in real-time bot protection across web, mobile, and APIs. It is effective for stopping large-scale automated account takeover attempts.
Key Features
- AI-based bot detection
- Real-time blocking
- API and mobile app protection
- Attack dashboards and alerts
Pros
- High bot detection accuracy
- Easy to deploy
- Strong API protection
Cons
- Limited post-login behavioral insight
- Less focus on human-driven ATO
Best Practices to Prevent Account Takeovers
Technology alone is not enough. Effective ATO prevention combines the right tools with a clear security strategy and continuous monitoring.
Use risk-based MFA, not static challenges: Trigger MFA based on device, location, and behavioral risk signals. This reduces user friction while adding stronger protection when activity looks suspicious.
Monitor login and post-login behavior continuously: Track session activity, account changes, transaction patterns, and unusual behavior after login to identify misuse before financial or data damage occurs.
Detect credential exposure early: Detect credential exposure early by monitoring breach sources and preventing credential stuffing attacks before abuse occurs.
Minimize false positives to protect UX: ATO prevention systems must balance security with usability by using contextual intelligence rather than rigid rules.
Layer bot detection, behavior analysis, and identity intelligence: Combining multiple signals creates stronger protection against both automated and human-driven attacks.
A strong ATO strategy reduces fraud risk while preserving customer trust. The goal is not just to block attacks, but to protect accounts without disrupting genuine users.
Conclusion
Account takeover attacks are not rare, they are persistent, automated, and designed to exploit valid credentials and trusted user behavior. Traditional controls alone cannot keep up with modern ATO tactics.
Effective prevention requires a layered approach that combines real-time detection, behavioral intelligence, bot mitigation, and adaptive authentication — all while maintaining a smooth user experience.
Choosing the right ATO prevention solution/tool is not just about stopping attacks. By investing in the right tools and strategies, businesses can protect users, preserve trust, and stay ahead of increasingly sophisticated attackers.
Get in touch with Sensfrx today to discover how it can protect your business operations and enhance customer confidence.
Frequently Asked Questions (FAQs)
By tracking reduced fraudulent logins, fewer account recovery cases, lower fraud losses, and minimal false positives after implementation.
Yes. Risk-based detection applies security controls only when activity appears suspicious, reducing unnecessary friction for genuine users.
No. Bot mitigation is important, but effective prevention also requires behavioral analysis and post-login monitoring.
Regularly. Attack tactics evolve quickly, so risk models should be continuously reviewed and refined.
Yes. ATO attacks affect businesses of all sizes, and scalable solutions make advanced protection accessible without complex setup.


